ALL-IN-ONE PLATFORM
esDynamic
Manage your attack workflows in a powerful and collaborative platform.
Expertise Modules
Executable catalog of attacks and techniques.
Infrastructure
Integrate your lab equipment and remotely manage your bench.
Lab equipments
Upgrade your lab with the latest hardware technologies.
PHYSICAL ATTACKS
Side Channel Attacks
Evaluate cryptography algorithms from data acquitition to result visualisation.
Fault Injection Attacks
Laser, Electromagnetic or Glitch to exploit a physical disruption.
Photoemission Analysis
Detect photon emissions from your IC to observe its behavior during operation.
EXPERTISE SERVICES
Evaluation Lab
Our team is ready to provide expert analysis of your hardware.
Starter Kits
Build know-how via built-in use cases developed on modern chips.
Cybersecurity Training
Grow expertise with hands-on training modules guided by a coach.
ALL-IN-ONE PLATFORM
esReverse
Static, dynamic and stress testing in a powerful and collaborative platform.
Extension: Intel x86, x64
Dynamic analyses for x86/x64 binaries with dedicated emulation frameworks.
Extension: ARM 32, 64
Dynamic analyses for ARM binaries with dedicated emulation frameworks.
DIFFERENT USAGES
Penetration Testing
Identify and exploit system vulnerabilities in a single platform.
Vulnerability Research
Uncover and address security gaps faster and more efficiently.
Code Audit & Verification
Effectively detect and neutralise harmful software.
Digital Forensics
Collaboratively analyse data to ensure thorough investigation.
EXPERTISE SERVICES
Software Assessment
Our team is ready to provide expert analysis of your binary code.
Cybersecurity training
Grow expertise with hands-on training modules guided by a coach.
INDUSTRIES
Semiconductor
Automotive
Security Lab
Gov. Agencies
Academics
Defense
Healthcare
Energy
ABOUT US
Why eShard?
Our team
Careers
FOLLOW US
Linkedin
Twitter
Youtube
Gitlab
Github
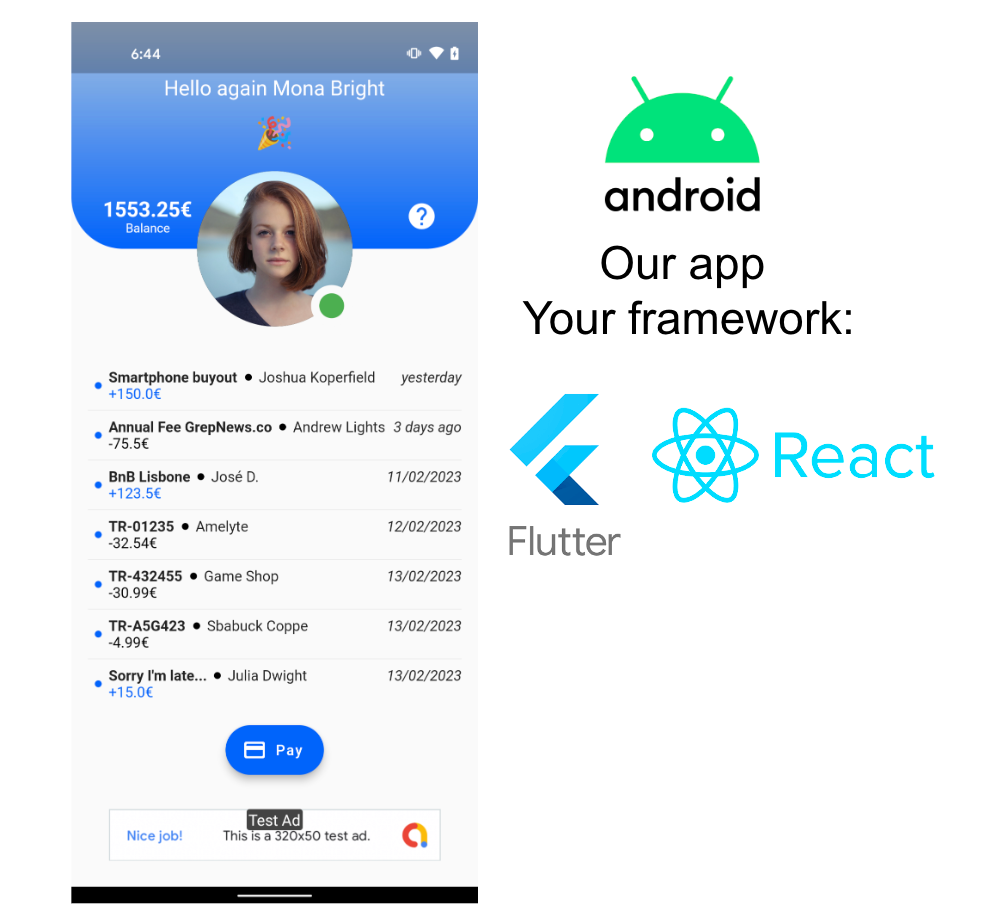
Mobile Application Defensive Development (Android)
The primary focus is understanding the typical weaknesses of mobile applications and the resulting know-how to implement sustainable code resilient to attacks. You choose your development framework (Flutter, React), we provide the mobile application.
The provided mobile application is non secure. You run static and dynamic testing with regards to a subset of the OWASP Mobile Application Security Testing Guide test cases. After identifying the different attack vectors and the potential attack paths that might be leveraged by an attacker, the trainees must plan and design the different protection layers to implement with the aim of shielding the application against reverse engineering and attacks.
Introduction to Mobile Application Risks
What are the risks from the user and business perspectives?
What is a sensitive asset in a mobile application?
Where are the sensitive assets stored? At-rest, in-transit?
The Attacker Toolbox
Introduction to rooting techniques and their consequences for mobile applications
What are the analysis techniques and tools that can be leveraged to reverse engineer an application and then attack it? Code instrumentation at runtime using a debugger or a code instrumentation framework; Static reverse engineering; App repackaging; Man-In-The-Middle.
How to statically reverse engineer the code of an Android application using IDA/GHIDRA/JADX-GUI/JEB.
How to instrument the code of an application at runtime on Android?
How to implement a Man-In-The-Middle attack on Android?
What about cross-platform mobile development frameworks? (e.g: React-Native, Flutter)
The Defender Toolbox
What must you be protected against? Runtime analysis techniques; Code and data tampering; Code reverse engineering; Network communication interception and tampering.
What must you ensure? The integrity, confidentiality and availability of sensitive data and code; The configuration of your app development tools; The configuration of your app; The configuration of the security tools that you bought for protecting your app
What are the security features that are provided by the Android platform and that one can leverage to protect its application?
Introduction to app shielding: detection and countermeasures
How to implement root detection? FRIDA detection? Debugging detection? MiTM attacks on Android? Application Package integrity check?
Introduction to code obfuscation: What to obfuscate? And how much / what are the different levels of obfuscation one can achieve?; What open source or commercial tools exist to obfuscate the code?
Hands-on exercises
Identify what are the different weaknesses of the insecure application by testing its resiliency against different attacks on our platform
Review the code of the insecure app in Android Studio
Plan and design the strategy that you want to implement to protect the application against identified weaknesses
Implement the different layers of protections that you have designed
Leverage at least one open source app shielding tool
Test the resiliency of your application against different attacks on our platform
Closing session with the trainer to present the strategy implemented, the difficulties encountered.
Practical information
Requirements: A training platform will be provided so that the trainees can access the training materials and the means to test the resiliency of their application.
Target: Mobile application developers.
Number of Trainees: 5 max trainees max per trainer.
Remote or On-Site.