AES-256 Climbing: Mastering Side-Channel Attacks on FPGAs

Introduction
When implemented in practice, side-channel attacks can be surprising. We developed this use case on an unprotected AES 256 embedded in a FPGA. We realized that a straightforward attack was not effective, which triggered our curiosity.
This blog post provides insights into the different steps of our analysis leading to the full secret exposure. It shows that the leakage model in the chip required some adjustment in the attack that we did not foresee. Besides, the illustration is made on an AES 256 showing that such cases require more sophistication than an AES 128.
This practical illustration confirms that side-channel attacks can be unpredictable, as they highly depend on the chip’s behavior. This necessitates specific attention from experts to thoroughly explore the model and adjust the attack strategy accordingly.
Setting the Base Camp
In this section, we delve into the specifics of our target: the FPGA board, the implementation of AES-256 and the context of the attack.

FPGA Implementation
Our setup features the ArtyS7-50 FPGA board from Digilent. This board embeds a Xilinx Spartan-7 FPGA, which offers approximately 50,000 logic cells and 2,700 Kbits of RAM, and operates at a clock frequency of up to 450 MHz. The Spartan-7 FPGA is chosen for its balance of performance and flexibility, providing an ideal platform for implementing the AES-256 encryption algorithm along with its key schedule.
Our AES-256 implementation assigns dedicated blocks to each round function, with each block containing its own registers. This design choice allows us to easily manage and analyze the behavior of each function –AddRoundKey, SubBytes, ShiftRows, and MixColumns– independently. The AES core functions are implemented straightforwardly, with no protections introduced.
Context
Our experimental context involves controlling the input plaintext while lacking control or knowledge of the output ciphertext. This setup mimics real-world scenarios where attackers may have access to the data being encrypted but not the encrypted output itself.
By leveraging our control over the input plaintext, we aim to exploit the physical leakages during the encryption process to recover the secret keys.
Find Where to Go
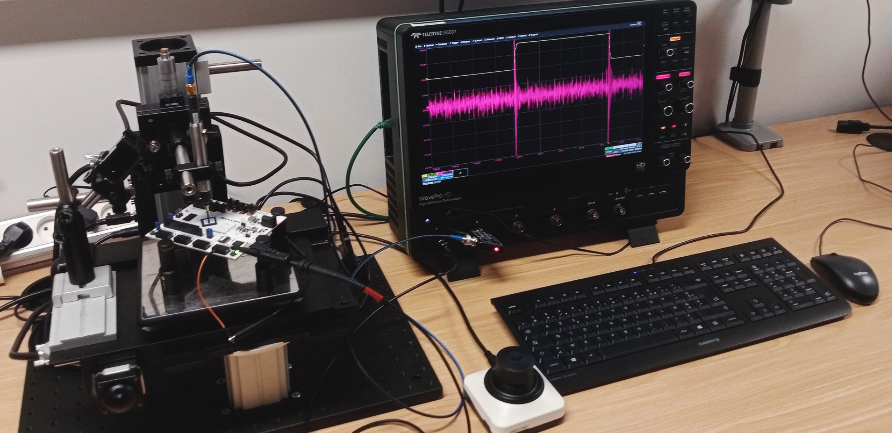
Now we are facing the FPGA with control only over the plaintext. To detect potential leakages, we mount an EM side-channel bench with a probe positioned over the Device Under Test (DUT). Our FPGA SCA AES-256 starter kit provides a step by step guide on how to create such detailed cartography.

EM cartography
We create an activity criterion to detect the AES activity along the X and Y axes. This involves scanning the DUT to identify the regions where AES operations are most active. As described in the below figure, we compute a Signal-to-Noise ratio coefficient by taking the Signal frame just after the trigger signal, and the noise frame before. Then, we compute the ratio of the standard deviation of both frame signals. A higher value of this ratio means that we obtain more signals.
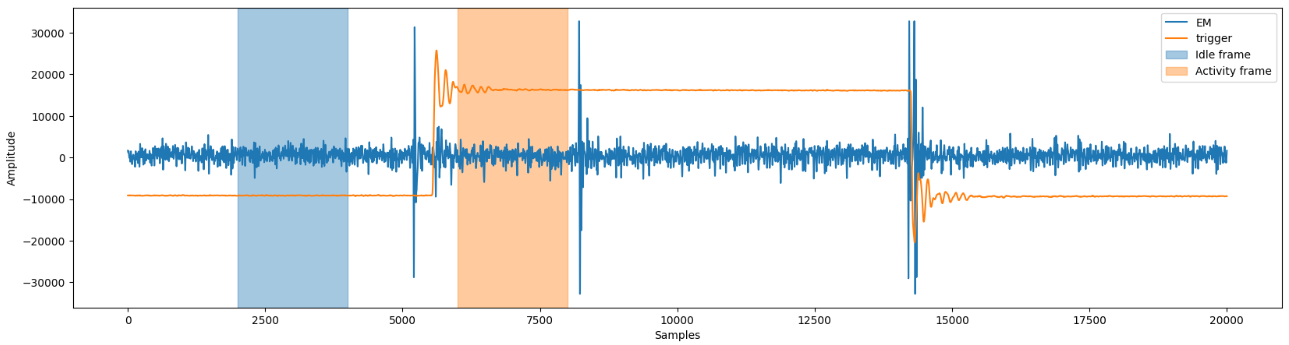
This analysis is performed for many probe locations over the DUT and color are associated to reveal the most active area. The below figure is extracted from our cartography tool included in esDynamic.
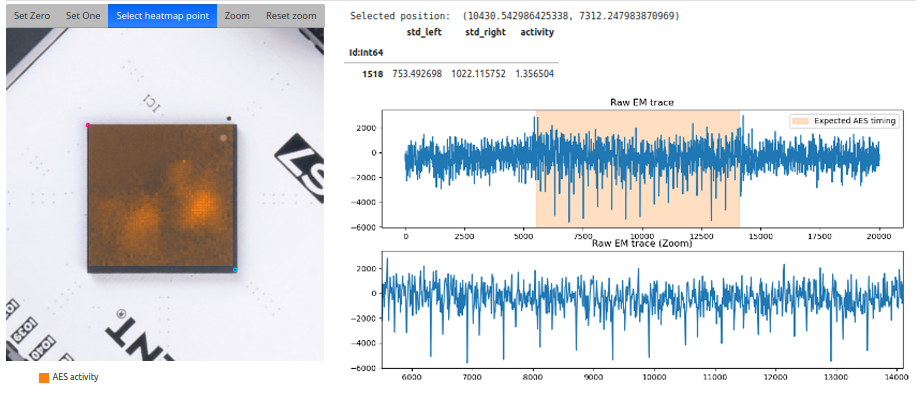
We can then focus our analysis on the most highlighted areas to exhibit side-channel leakages.
T-test
Once we identify a promising probe location based on the XY EM cartography, we proceed with acquiring EM traces. We acquire traces under two scenarios: first, using a fixed key and a fixed plaintext, and second, using a fixed key but with random plaintext inputs for each encryption cycle. This comparison allows us to identify any dependencies in the electromagnetic emissions that correlate with changes in plaintext input.
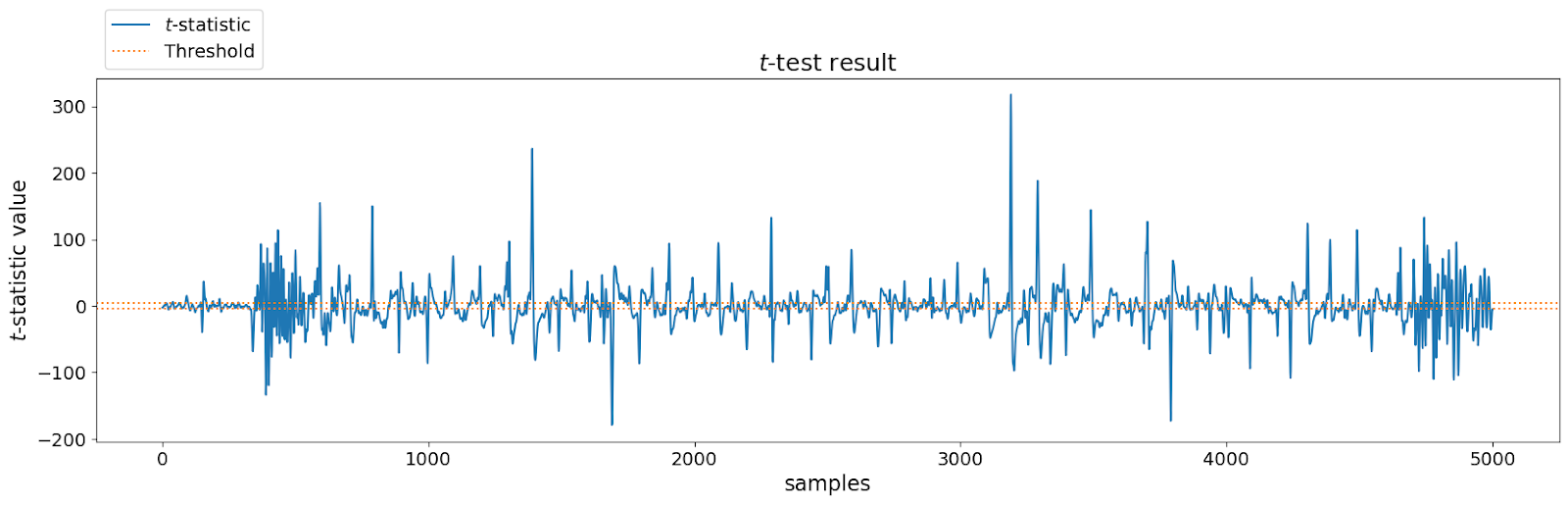
While the T-test reveals some leakages, it does not provide specific details on their nature and origin. We need to go deeper using selection functions to uncover more insight into these leakages.
Which leakages?
A correlation leakage analysis on the SubByte output is performed using the Hamming Weight model and reveals no obvious failure. Below, you'll find an image taken from our esDynamic solution, which features the selection function definition and the visualization of its results.

The hardware implementation splits the AES core functions into blocks, each with a dedicated "state register" (FPGA signal). When a function (e.g., SubBytes) is executed, the result is an FPGA signal output that replaces the previous one, as illustrated below by the State_SubBytes marker.
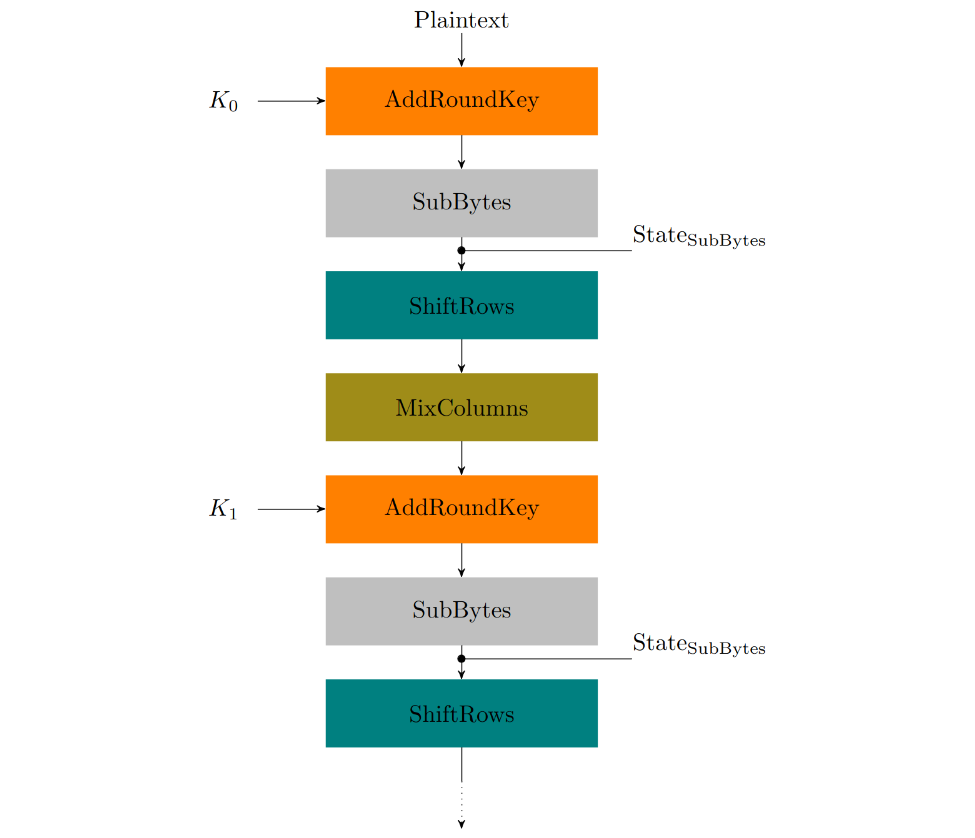
We will then assess if this "signal replacement" causes leakages, instead of the function computation itself.
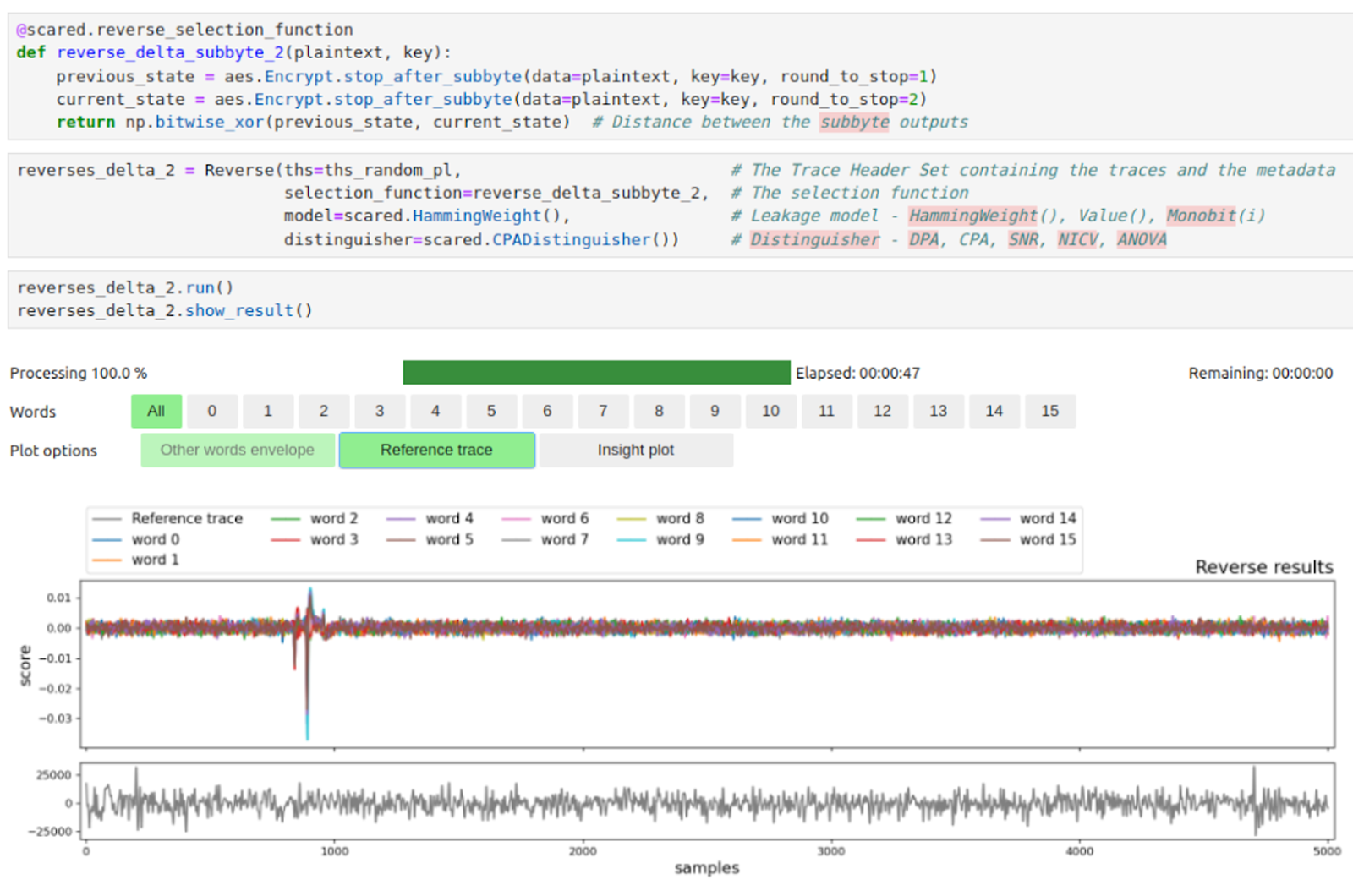
We discover leakages in Delta between state functions from transitions of round one to two, as shown by the correlation peaks around samples 900.
Then, Delta leakages occur when the state transitions erase residual information from previous encryption rounds. By using our complete knowledge on the plaintext and the key during the characterization step, we check this statement by targeting the Delta between:
- SubByte output at round one.
- SubByte output at round fourteen of the previous AES encryption.
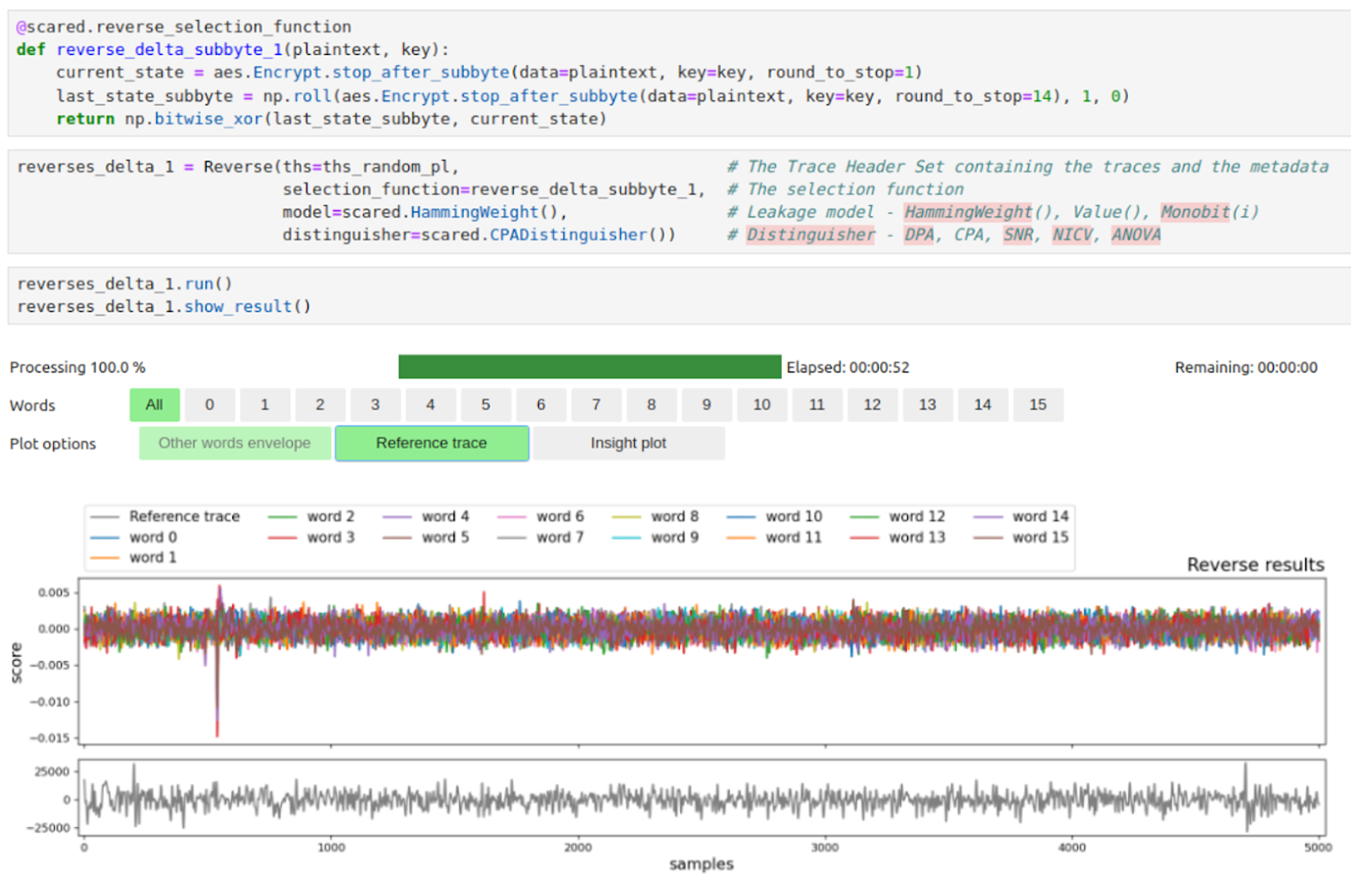
This discovery is crucial as it highlights specific areas where the side-channel attack can exploit these transitions to extract sensitive information. A nuanced strategy is essential for fully exploiting these leakages.
Climbing the Key Route
To target the first round key of AES-256, our approach hinges on exploiting the operations of the initial and first AES rounds. By leveraging our control over the plaintext input, we can partially control the initial values stored in the registers of each round function.
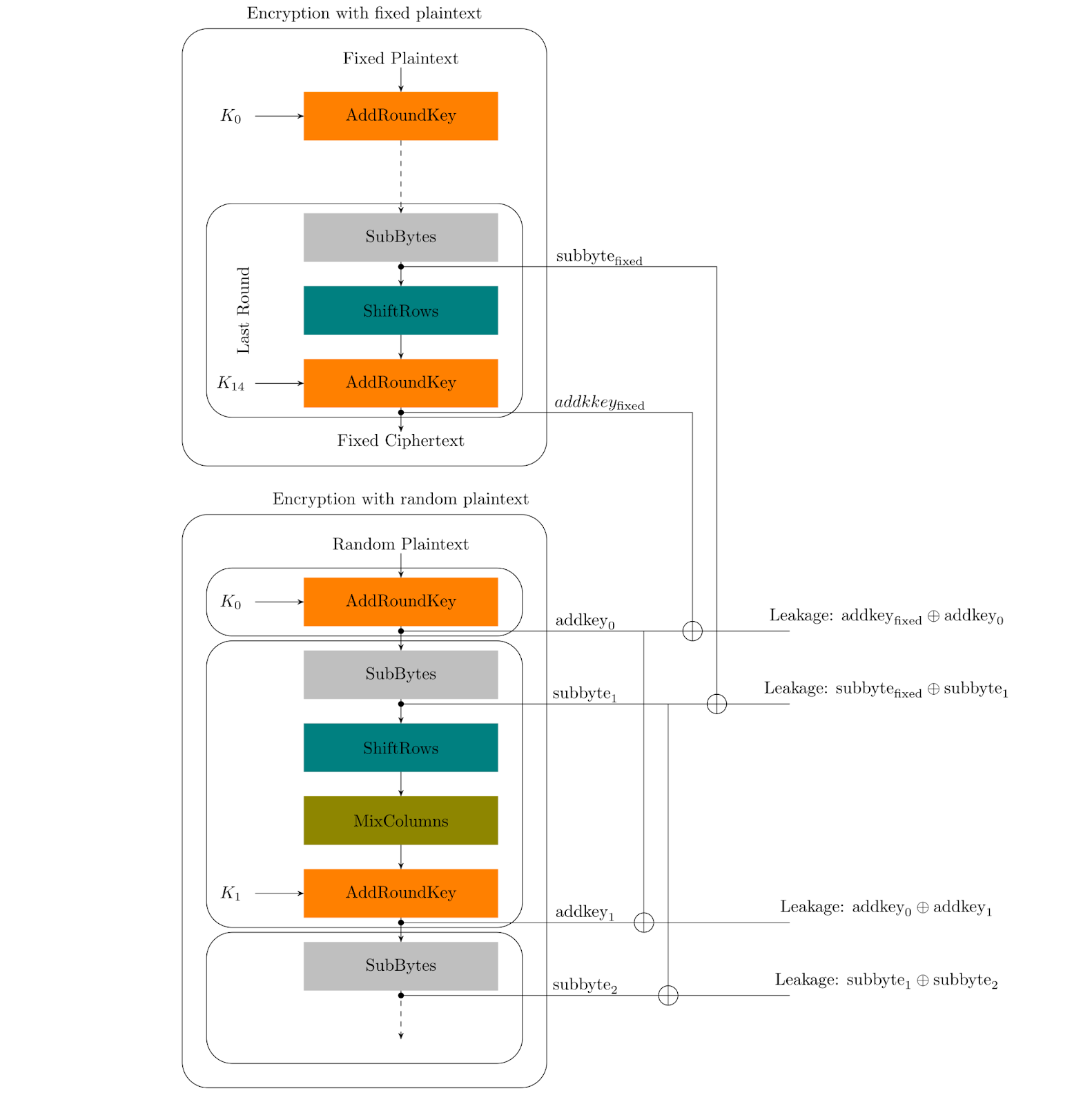
Chosen Plaintext Strategy
Our strategy involves interleaving two distinct executions of AES-256:
- Fixed Plaintext Execution: In this phase, we use a fixed plaintext to initialize the registers of the last AES round to unknown, but consistent values.
- Random Known Plaintext Execution: Following the fixed plaintext phase, we execute AES-256 with randomly drawn known plaintexts. This looks like a classical side-channel attack method.
The strategy is illustrated as below:
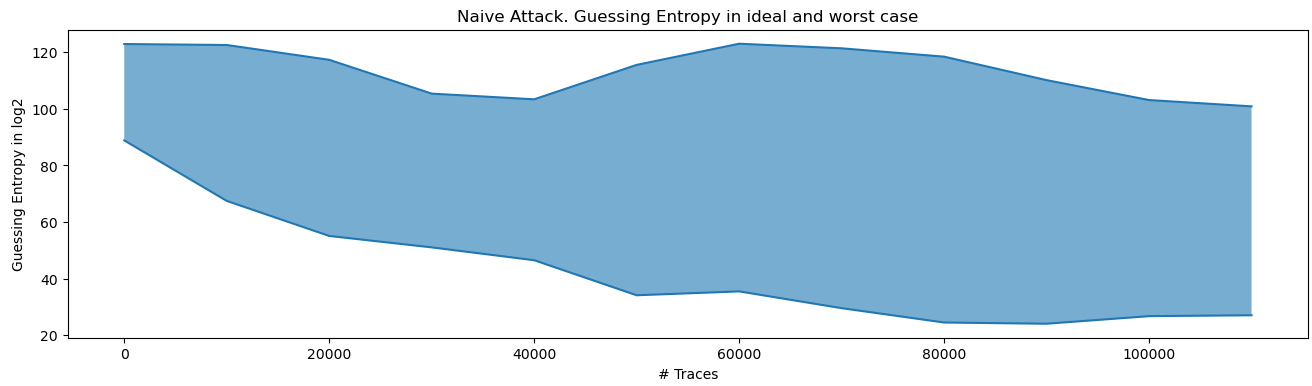
Direct attack: Partial Byte Recovery
In our first attempts, we employ a Correlation Power Analysis (CPA) attack. However, the attack fails to recover all key bytes due to the nature of the leakages. Specifically, the leakages manifest as variations in Hamming Distance between the round intermediate value (computed by the selection function) and a fixed non-zero register value. Let's utilize esDynamic to assess the guessing entropy resulting from the direct attack.
Reaching the Summit
In addition to direct attacks, we develop advanced techniques to fully exploit the discovered leakages, leading to a complete key recovery.
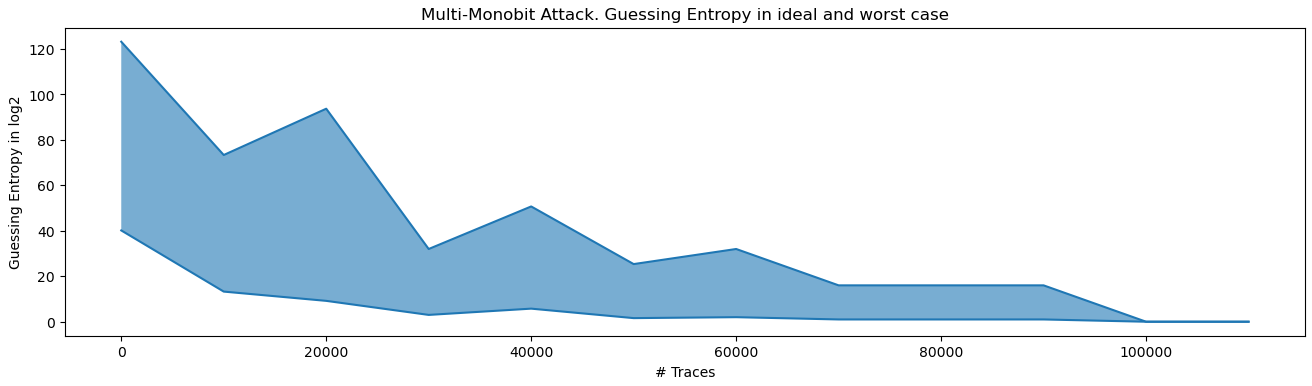
Multi-Monobit Attack
The multi-monobit attack leverages the correlation between power consumption traces and each bit of the intermediate values. Let us illustrate the situation with the figure below.
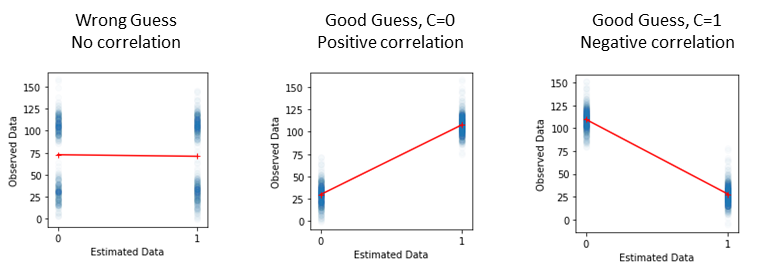
The key bit value is XORed with an unknown constant C. When the key bit guess is incorrect, the correlation between the traces and the intermediate bit value remains low. However, when the key bit guess is correct, a correlation appears. Moreover, if the constant bit value C is 0, the correlation is positive; but if C = 0, the correlation is negative (we recover the opposite bit). We exploit all eight monobit models by computing correlations for each of them, then we merge the results by averaging all scores. By this way, all monobit attacks (indifferent to constant C), lead to enhanced side-channel analysis, allowing for a complete key recovery.
Mixed Secret-Unknown Attack
In this approach, the last state register from the previous AES round (run with fixed plaintext) is treated as a fixed unknown “key”. By performing a 16-bit guess attack, we can effectively recover the AES first-round key.

Through these advanced attack strategies, we demonstrate the capability to not only enhance the success rate of key recovery but also to address the intricacies of side-channel leakages in a more sophisticated manner.
Complete Key Recovery
After recovering the first 16-byte key of the AES-256 key, we targeted the second part by focusing on the second round. Specifically, we exploited the erasure of the values of the first round by the second round. This attack did not require the interleaved chosen plaintext strategy because the registers are only updated within the same AES execution, eliminating the need to fix the registers from the previous round.

Conclusion
Our exploration into side-channel attacks on FPGA implementations of AES-256 highlights the intricacies and challenges involved. By leveraging control over the plaintext, we detected and analyzed EM leakages, focusing on the transitions between encryption rounds. Initial attacks using a direct CPA approach yielded partial byte recovery due to the nature of the leakages. Advanced attacks proved more successful, recovering both the first and second round keys.
Finally, the second part of the AES-256 key is recovered by the way of a direct CPA attack.
We demonstrate that even high data dependencies revealed by a T-test are not straightforward to understand. After clear leakage characterization, a fine-tuned strategy must be established to exploit the high potential of these leakages, ultimately leading to a successful attack.
All the material, including the FPGA and AES-256 bitstream, along with the complete set-up, analysis scripts, and various attack techniques, can be found in our FPGA SCA AES-256 starter kit.


