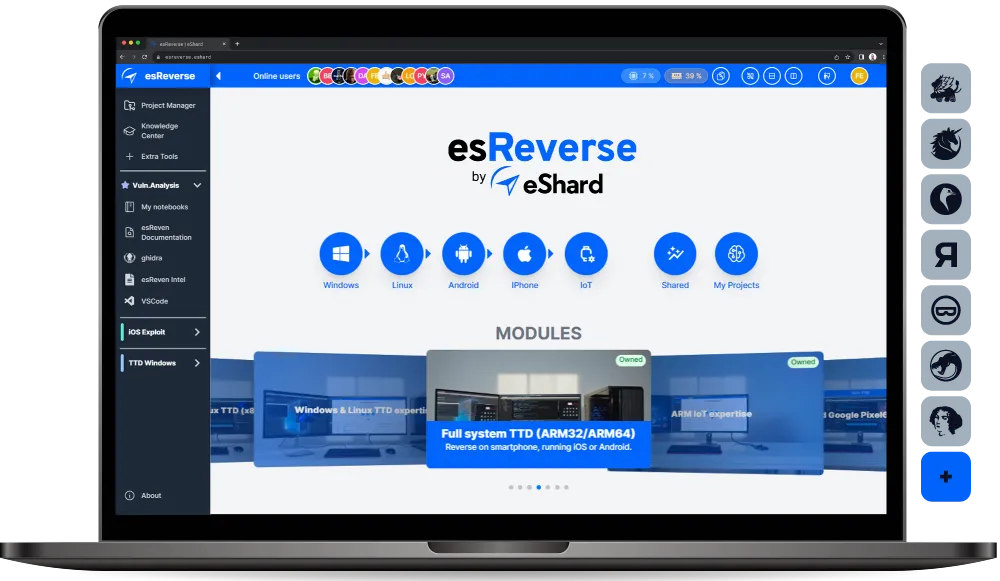
One environment
for all investigations


Project-based organization
Each investigation is a project with its own datasets, tool configurations, team access, and findings. Switch between analyses without rebuilding your environment.
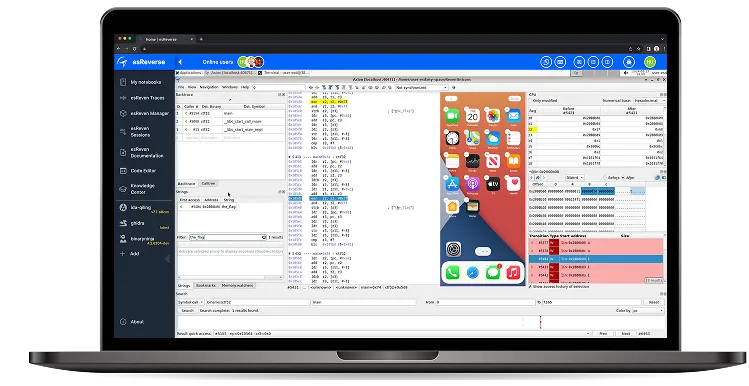
Specialized dynamic
analysis tools
Time Travel Debugging and virtual environments for iOS, Android, Windows, Linux, and IoT, with complete system visibility across every platform.
Tool integration
Connect your debuggers, disassemblers, and custom tools in one environment. Combine them, switch between them, and run your analysis within the esReverse environment.
Shared expertise
Turn individual investigations into team knowledge. Document findings, reuse workflows, and enrich your analysis with our catalogue of real-world attack techniques.
Built for real-world security investigations
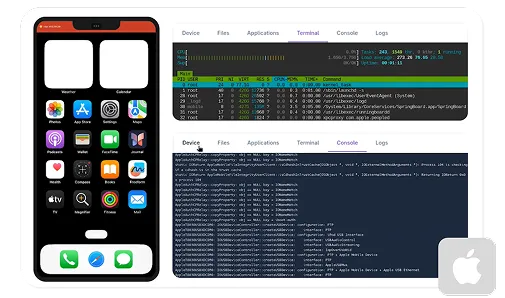
iOS Security Investigations
Investigate iOS apps and system behavior without physical devices or jailbreaks.





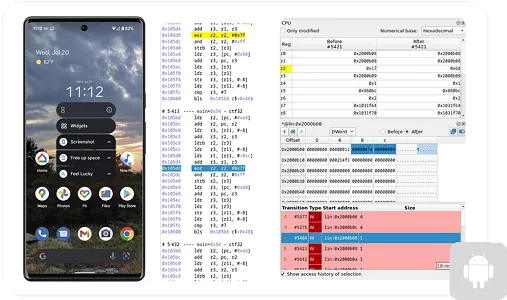
Android Security Investigations
System-level analysis with rooted virtual environments.





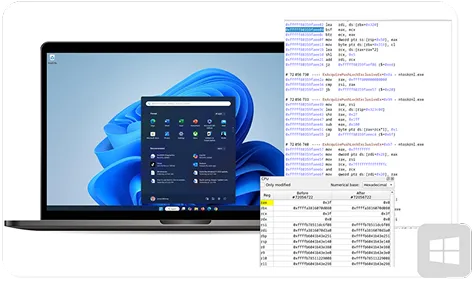
Windows Malware Investigation
Full kernel and user-space visibility with Time Travel Analysis.





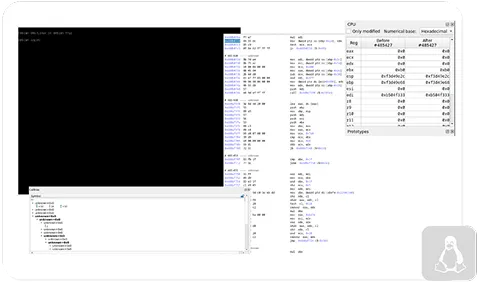
Linux System Debugging
Kernel debugging with Time Travel Analysis across architectures.





IoT Firmware
Analysis
ARM emulation with Time Travel Analysis for embedded systems.





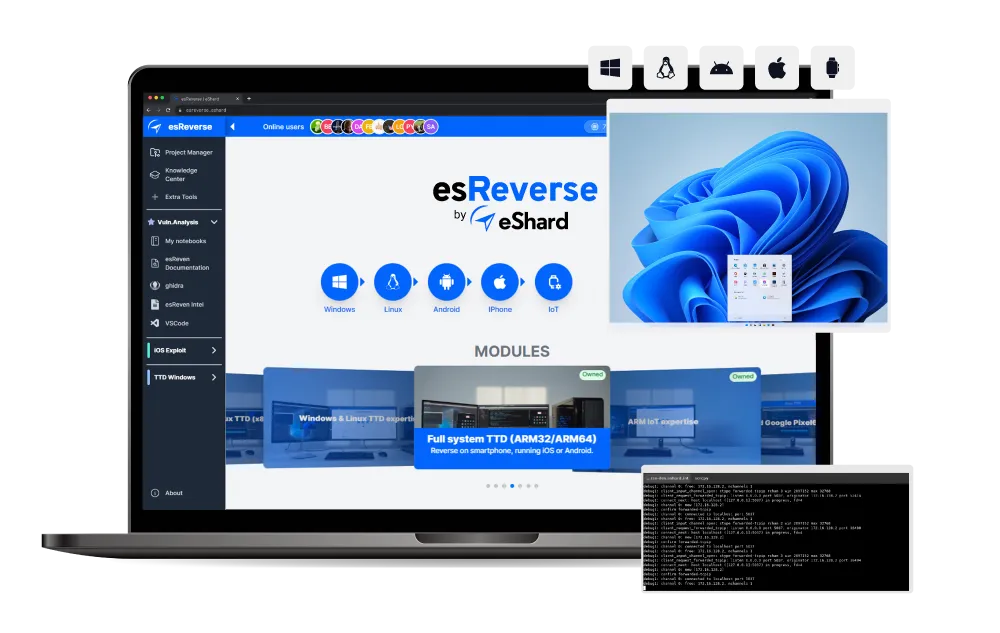
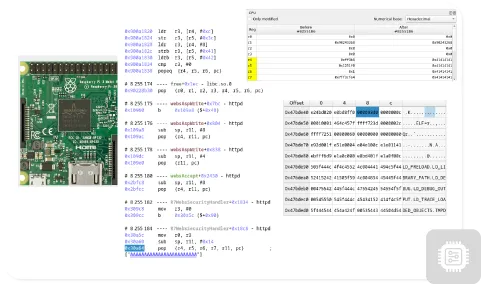
Full-system Time Travel Debugging
Full-system Time Travel Debugging and targeted binary instrumentation
Understand complex behavior, uncover hidden vulnerabilities, and replay any moment in a program's lifetime with complete system visibility. When needed, an AI agent is on hand to assist your workflow.
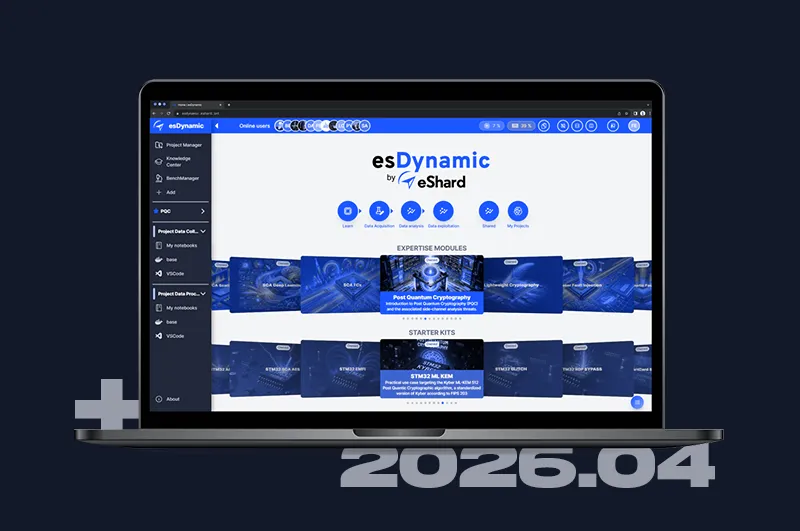
Start from proven methodologies
Access ready-to-use security methodologies, extend them with your own findings, and build reusable attack templates that empower your entire reverse engineering team.
Advanced binary analysis techniques
Master vulnerability research through interactive tutorials and proven methodologies focused on real-world binary analysis and reverse engineering.
Embedded & IoT security
Identify vulnerabilities in connected devices by combining full-system firmware emulation, targeted fuzzing, and Time Travel Debugging for precise crash analysis.
Access esReverse
for your investigations
Leave your details and a specialist will reach out to schedule a session tailored to your analysis use case.
Frequently Asked Questions
The platform includes innate tools like VS Code and Jupyter, emulators, a time travel debugging tool, and integrations with industry-standard reverse engineering tools such as Binary Ninja, Ghidra, IDA, Frida, BinDiff, and GDB.
No, you can add as many people as you'd like to your project. If you want to manage multiple projects, you can expand with a license that includes the Project Manager feature. Licenses are per server.
esReverse is a web-based application deployed on-premises (via Docker or Virtual Appliance) or hosted in your private cloud.
Yes. Easily connect your existing tools and build custom workflows so that esReverse adapts perfectly to your environment, not the other way around.