ALL-IN-ONE PLATFORM
esDynamic
Manage your attack workflows in a powerful and collaborative platform.
Expertise Modules
Executable catalog of attacks and techniques.
Infrastructure
Integrate your lab equipment and remotely manage your bench.
Lab equipments
Upgrade your lab with the latest hardware technologies.
PHYSICAL ATTACKS
Side Channel Attacks
Evaluate cryptography algorithms from data acquitition to result visualisation.
Fault Injection Attacks
Laser, Electromagnetic or Glitch to exploit a physical disruption.
Photoemission Analysis
Detect photon emissions from your IC to observe its behavior during operation.
EXPERTISE SERVICES
Evaluation Lab
Our team is ready to provide expert analysis of your hardware.
Starter Kits
Build know-how via built-in use cases developed on modern chips.
Cybersecurity Training
Grow expertise with hands-on training modules guided by a coach.
ALL-IN-ONE PLATFORM
esReverse
Static, dynamic and stress testing in a powerful and collaborative platform.
Extension: Intel x86, x64
Dynamic analyses for x86/x64 binaries with dedicated emulation frameworks.
Extension: ARM 32, 64
Dynamic analyses for ARM binaries with dedicated emulation frameworks.
DIFFERENT USAGES
Penetration Testing
Identify and exploit system vulnerabilities in a single platform.
Vulnerability Research
Uncover and address security gaps faster and more efficiently.
Code Audit & Verification
Effectively detect and neutralise harmful software.
Digital Forensics
Collaboratively analyse data to ensure thorough investigation.
EXPERTISE SERVICES
Software Assessment
Our team is ready to provide expert analysis of your binary code.
Cybersecurity training
Grow expertise with hands-on training modules guided by a coach.
INDUSTRIES
Semiconductor
Automotive
Security Lab
Gov. Agencies
Academics
Defense
Healthcare
Energy
ABOUT US
Why eShard?
Our team
Careers
FOLLOW US
Linkedin
Twitter
Youtube
Gitlab
Github
The Side Channel Chronicles #1: A bit of history
If you think that the resistance of a cryptographic algorithm relies only on the underlying recognized hard problem, you are wrong! The real-world implementation of these algorithms on electronic devices opens up vulnerabilities that hackers can exploit through Side channel attacks.
Contrary to popular belief, the robustness of cryptographic algorithms isn't just about the complexity evaluated by classical cryptanalysis. Side channel attacks present a significant threat by leveraging unintended information leakage from computing systems. This leakage can occur through various channels such as power consumption, electromagnetic radiation, execution timing, or even sound.
How did all of this started?
A brief history of Side channel Attacks
Side channel attacks were first identified in the late 20th century when researchers found that the physical execution of cryptographic algorithms could inadvertently expose sensitive data. Unlike traditional attacks that target the algorithm's theoretical strength, Side channel attacks exploit "side information" exposed during cryptographic operations. For instance, power consumption patterns or electromagnetic emissions can reveal critical insights into the computations being performed.
These side channels are often linked to the Hamming Weight (HW) or Hamming Distance (HD) of intermediate data processed by the algorithm. In side channel analysis, the information collected during operations like encryption, decryption, or signature generation is referred to as traces.
![]()
The impact of Side Channel Attacks
Side channel attacks have demonstrated remarkable effectiveness against a variety of devices, from smart cards and embedded systems to modern CPUs. An unprotected Advanced Encryption Standard (AES) implementation can be compromised in minutes by analyzing a few hundred power traces, whereas no practical attack surpasses brute force for AES. Similarly, a poorly implemented RSA algorithm can reveal its secret exponent through a single power trace observation.
Developing countermeasures
As awareness of side channel attacks grew, researchers and industry practitioners prioritized developing robust countermeasures. These efforts aim to mitigate the impact of side channel attacks while preserving performance and usability. Techniques like randomizing inner computations of cryptographic algorithms disrupt the correlation between observable side channels and the sensitive information targeted by attackers.
Implementing cryptographic algorithms with side channel resistance is an ongoing challenge. Addressing all potential leakage sources comprehensively requires continual research, collaboration, and vigilance. As technology advances and adversaries refine their methods, staying ahead in the evolving landscape of side channel attacks is crucial.

Efficient tools for Side Channel Analysis
The field of side channel analysis has seen the development of sophisticated tools designed to aid analysts in their efforts.
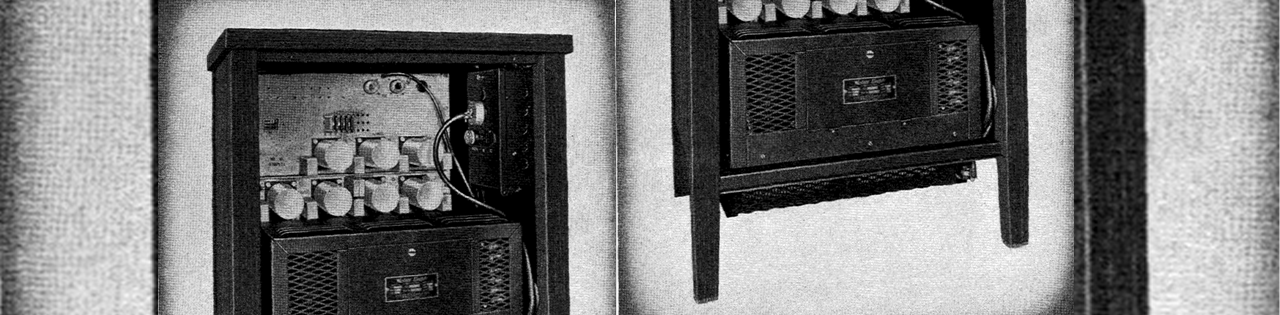
Oscilloscopes (see image above), for instance, are critical for monitoring the power consumption and electromagnetic emissions of target devices. These high-precision instruments allow analysts to capture traces that reveal the side channels through which sensitive data may be leaking.
Moreover, specialized equipment like electromagnetic probes can capture subtle emissions that ordinary tools might miss, and advanced signal processing software can enhance the clarity of the captured data. These tools are essential for both identifying weaknesses in cryptographic implementations and developing effective countermeasures.
Software tools are equally important, processing and analyzing these traces to uncover patterns and vulnerabilities. Among these, esDynamic stands out for its powerful features. It performs detailed trace analysis and applies statistical methods to detect vulnerabilities. With a collaborative environment and intuitive interface, esDynamic simplifies data visualization and identifies correlations and anomalies. Its advanced algorithms efficiently process large datasets, ensuring no leakage is missed.
✳ Next step: Setting up a lab
In the next post of "The Side Channel Chronicles," we will explore the practical aspects of setting up a side channel analysis lab. We'll cover the essential tools and equipment, data acquisition techniques, and the initial steps in analyzing power and electromagnetic side channels.
Whether you're a seasoned security professional or new to the field, our next post will provide valuable insights to deepen your understanding of these sophisticated attacks and how to defend against them.