ALL-IN-ONE PLATFORM
esDynamic
Manage your attack workflows in a powerful and collaborative platform.
Expertise Modules
Executable catalog of attacks and techniques.
Infrastructure
Integrate your lab equipment and remotely manage your bench.
Lab equipments
Upgrade your lab with the latest hardware technologies.
PHYSICAL ATTACKS
Side Channel Attacks
Evaluate cryptography algorithms from data acquitition to result visualisation.
Fault Injection Attacks
Laser, Electromagnetic or Glitch to exploit a physical disruption.
Photoemission Analysis
Detect photon emissions from your IC to observe its behavior during operation.
EXPERTISE SERVICES
Evaluation Lab
Our team is ready to provide expert analysis of your hardware.
Starter Kits
Build know-how via built-in use cases developed on modern chips.
Cybersecurity Training
Grow expertise with hands-on training modules guided by a coach.
ALL-IN-ONE PLATFORM
esReverse
Static, dynamic and stress testing in a powerful and collaborative platform.
Extension: Intel x86, x64
Dynamic analyses for x86/x64 binaries with dedicated emulation frameworks.
Extension: ARM 32, 64
Dynamic analyses for ARM binaries with dedicated emulation frameworks.
DIFFERENT USAGES
Penetration Testing
Identify and exploit system vulnerabilities in a single platform.
Vulnerability Research
Uncover and address security gaps faster and more efficiently.
Code Audit & Verification
Effectively detect and neutralise harmful software.
Digital Forensics
Collaboratively analyse data to ensure thorough investigation.
EXPERTISE SERVICES
Software Assessment
Our team is ready to provide expert analysis of your binary code.
Cybersecurity training
Grow expertise with hands-on training modules guided by a coach.
INDUSTRIES
Semiconductor
Automotive
Security Lab
Gov. Agencies
Academics
Defense
Healthcare
Energy
ABOUT US
Why eShard?
Our team
Careers
FOLLOW US
Linkedin
Twitter
Youtube
Gitlab
Github
esReven 2023.04 is out!
eShard is pleased to announce that esReven version 2023.04 is now out!
This article covers the changes introduced in this release. In summary, this second version released by eShard focuses on 2 areas:
- Quality-of-life updates to the product.
- Introduction of two new knowledge modules.
Quality-of-life updates to the product
- First of all, esReven is now the easiest to install it has ever been! The packaging matures as we take more and more environments into account: you can now install & run esReven with an up-to-date
docker composeplugin, on no-execute partitions, with noptracerights, you can configure proxies, and so on. - We also addressed a number of small issues that smooth out the web interface experience: the log out/log back in workflow now works as expected, we fixed issues that required the user to refresh the page, etc.
- Lastly, we made a few improvements to the esReven engine and its environment: the ASM stub is easier to discover and use, and now supports Rust as well. Bugs have also been fixed in the API and other places.
You can read the full list of changes in this version's release notes.
Subscription-based knowledge modules
Following the path set in the previous version, in parallel to this version we are introducing the first two subscription-based knowledge-base modules. These must be purchased separately from your esReven license, and will get new content regularly.
Advanced Usage How-tos
These how-tos will provide straightforward guides that cover situations where translating the intent of the reverse engineer into a set of tasks is not trivial. They are intended for those who wish to refine their esReven skills to tackle advanced use cases and be more efficient with the platform.
At the time of this release, we have focused on addressing advanced recording situations, as well as networking options:
- Recording non-trivial environments: discover how to efficiently record many use-cases with general strategies and actionable information to get you started quickly.
- Overview of the tools at our disposal for recording.
- Strategy: recording a standalone application as it loads data (file, URL, etc.).
- Strategy: recording a standalone application as I communicate with it (via IPC, network or other).
- Strategy: the crash (or procedure) is non-deterministic or not 100% reliable.
- How to: every method to stop the recording when a process exits, crashes, or when the OS crashes.
- How to to inject code in a program to control its behavior or its recording.
- Advanced target VM networking: discover various networking possiblities for your target VM and the proper QEMU options you can use, covering more advanced use cases than the default.
Applied Algorithms & Tools
In this module, we introduce comprehensive tools built on top of the esReven framework. These tools will help you better leverage esReven to answer questions more effectively, while teaching you about the approach taken.
Tools are documented such that they can be adapted if necessary, and, when applicable, provide their functionality as a library so other scripts can be built on top of them.
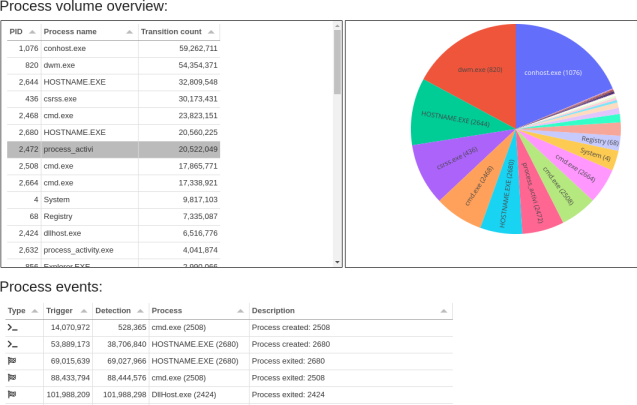
At the time of this release, we have focused on extracting valuable information from Windows traces with two important tools:
- Process activity (Windows): This tool notebook presents the activity on files on a trace: file creation, accesses, etc.
- File Activity (Windows): This tool notebook presents an overview of the general process activity in a trace: process starts, exits, crashes.
Along with the tools come Python libraries to exploit the data in your own scripts, as well as knowledge notebooks that explain the approach taken.
And what now?
And that's it for this release! You can find the full list of improvements and fixes in the version's release notes.
Interested in knowing more about knowledge modules?
Contact us to get the detailed content of those modules and how to get access to them.
Want to try the product?
- We provide an extensive set of online demos, which constitute a good first step with tutorials available in most. However, they are based on the previous REVEN version for the time being.
- Want to try the new esReven? Contact us!